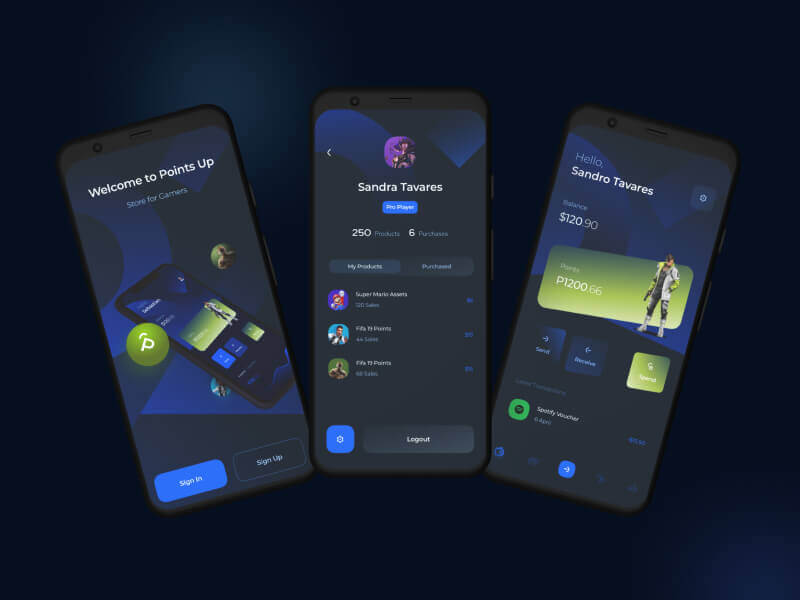
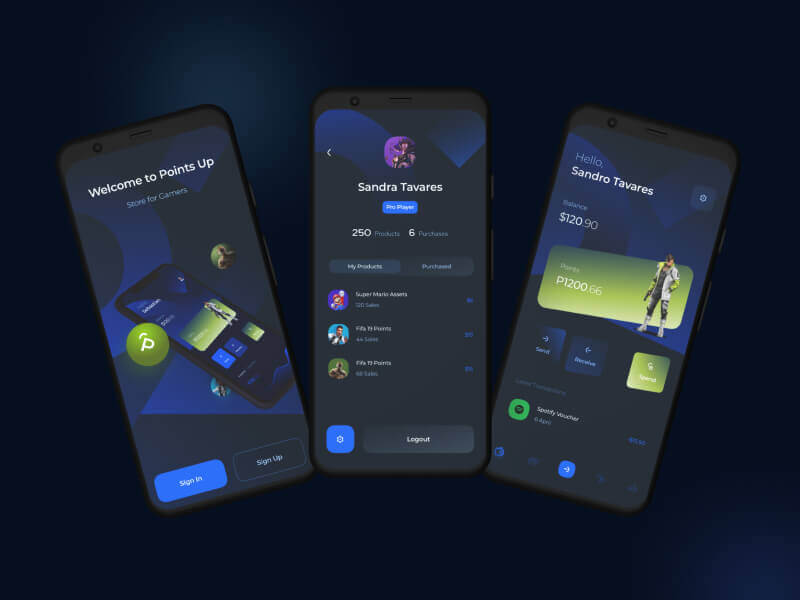
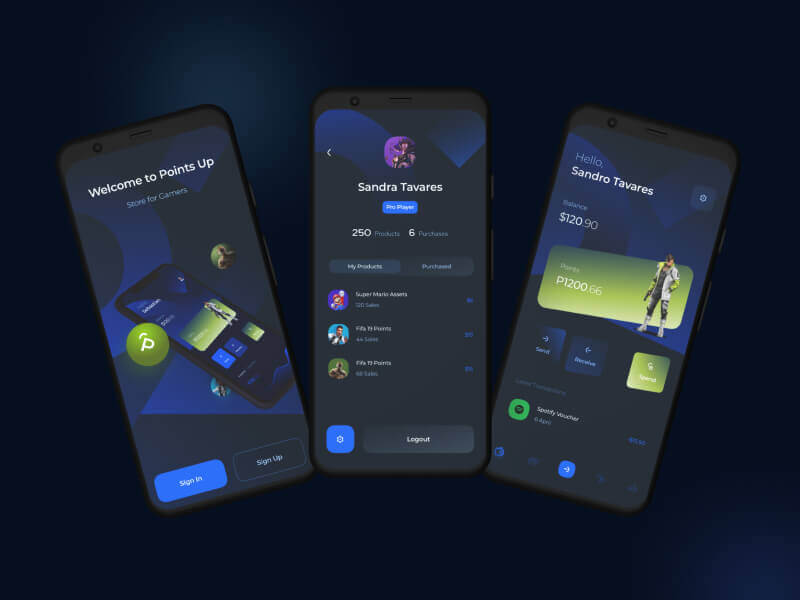
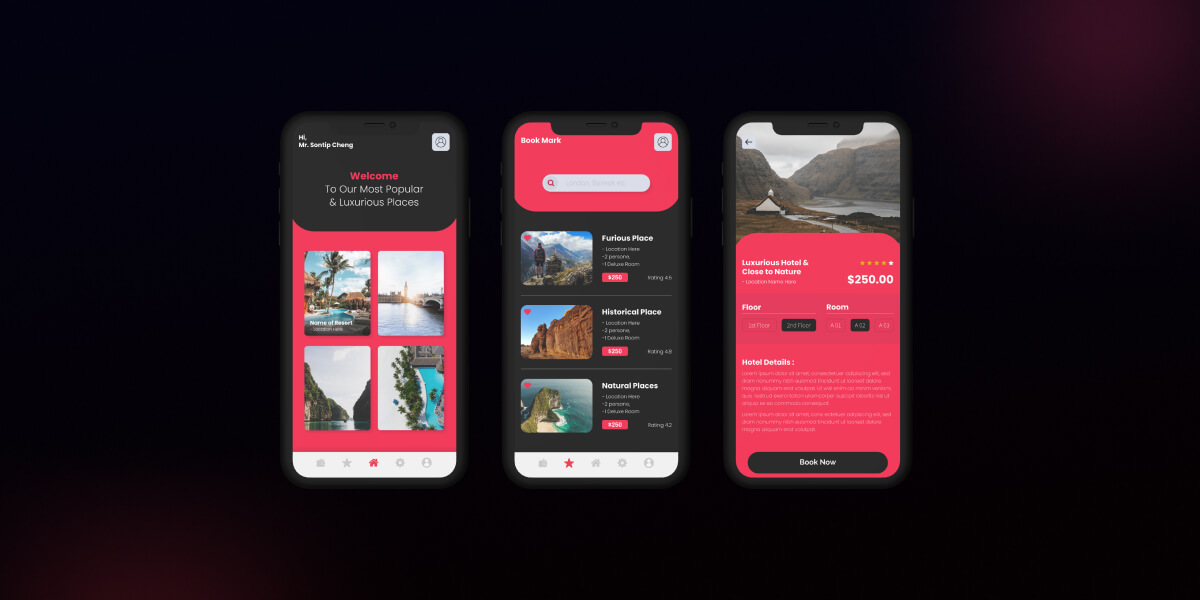
NFT Dashboard Application Development.
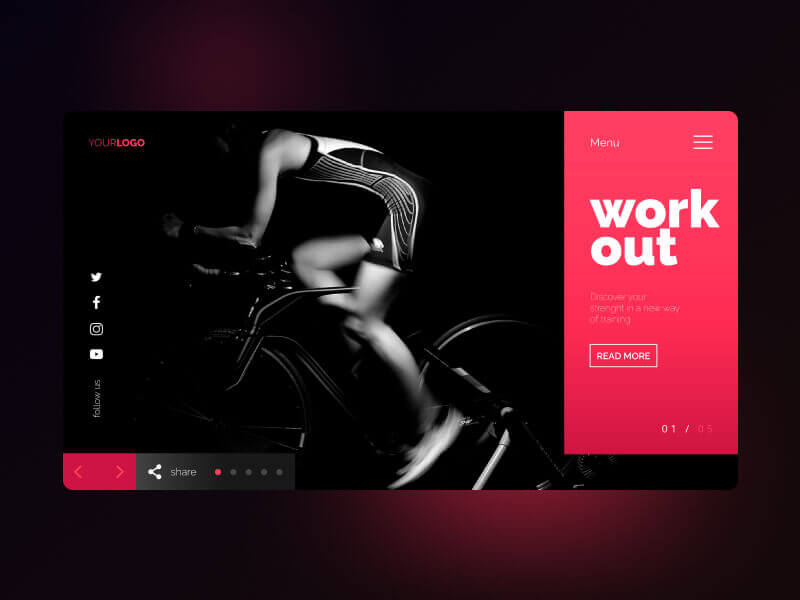
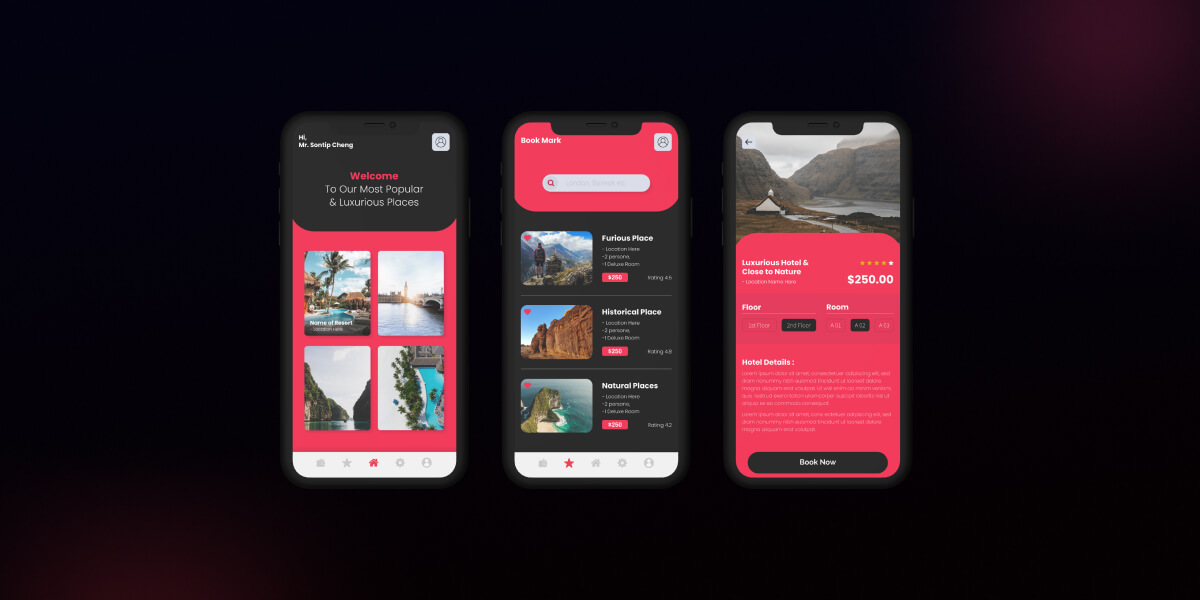
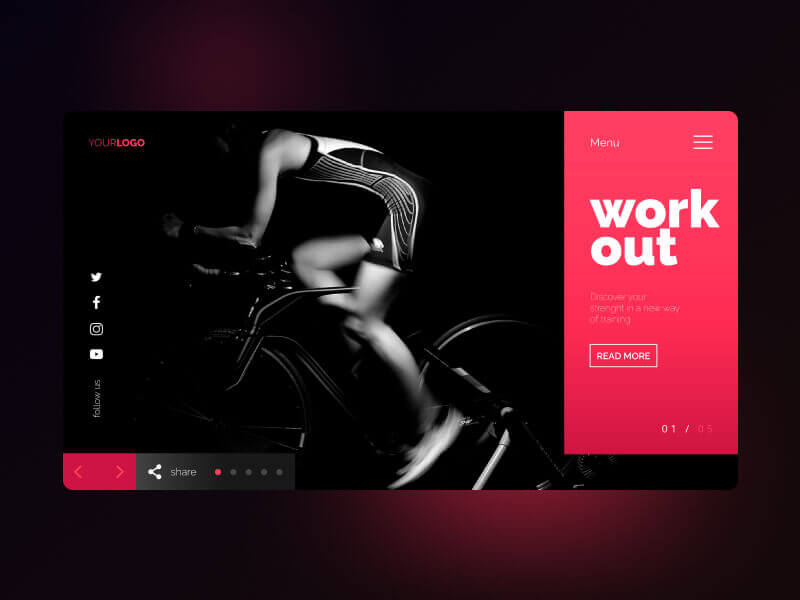
Through a wide variety of mobile applications, we’ve developed a unique visual system.
- Client George Wallace
- Date 15 June 2022
- Services Web Application
- Budget $100000+
We use animation as a third dimension by which to simplify experiences and kuiding thro each and every interaction. We are not adding motion just to spruce things up, but doing it in ways that.

We’ll handle everything from to app development process until it is time to make your project live.
Using our expertise in mobile application development to create beautiful pixel-perfect designs.
Your website ranking matters. Our SEO services will help you get to the top of the ranks and stay there!
Get the best results with expert Meta Ads setup and optimization
Stand out online with powerful and creative social media marketing
Through a wide variety of mobile applications, we’ve developed a unique visual system.
There are always some stocks, which illusively scale lofty heights in a given time period. However, the good show doesn’t last for these overblown toxic stocks as their current price is not justified by their fundamental strength.
A strategy is a general plan to achieve one or more long-term. labore et dolore magna aliqua.
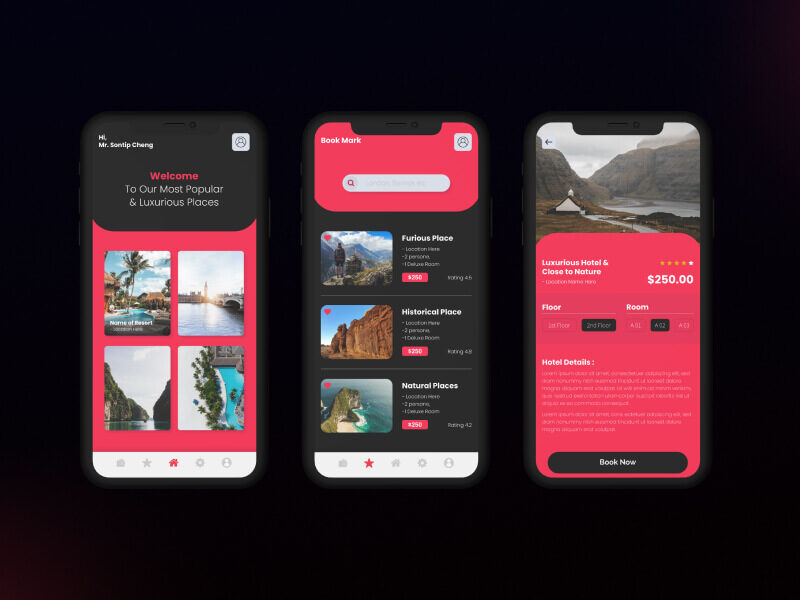
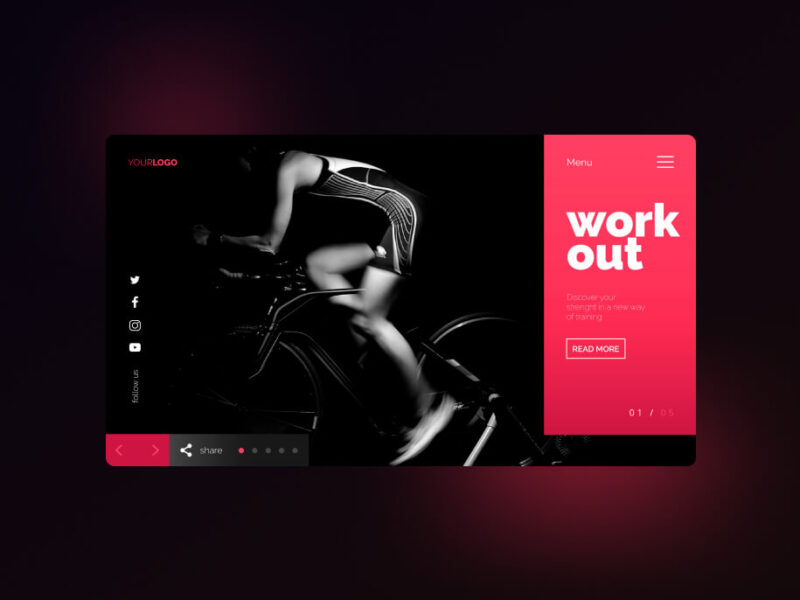
UI/UX Design, Art Direction, A design is a plan or specification for art. which illusively scale lofty heights.
User experience (UX) design is the process design teams use to create products that provide.
Toxic companies are usually characterized by huge debt loads and are vulnerable to external shocks. Accurately identifying such bloated stocks and getting rid of them at the right time can protect your portfolio.
Overpricing of these toxic stocks can be attributed to either an irrational enthusiasm surrounding them or some serious fundamental drawbacks. If you own such bubble stocks for an inordinate period of time, you are bound to see a massive erosion of wealth.

However, if you can precisely spot such toxic stocks, you may gain by resorting to an investing strategy called short selling. This strategy allows one to sell a stock first and then buy it when the price falls.
While short selling excels in bear markets, it typically loses money in bull markets.
So, just like identifying stocks with growth potential, pinpointing toxic stocks and offloading them at the right time is crucial to guard one’s portfolio from big losses or make profits by short selling them. Heska Corporation HSKA, Tandem Diabetes Care, Inc. TNDM, Credit Suisse Group CS,Zalando SE ZLNDY and Las Vegas Sands LVS are a few such toxic stocks.Screening Criteria
Here is a winning strategy that will help you to identify overhyped toxic stocks:
Most recent Debt/Equity Ratio greater than the median industry average: High debt/equity ratio implies high leverage. High leverage indicates a huge level of repayment that the company has to make in connection with the debt amount.
Through a wide variety of mobile applications, we’ve developed a unique visual system and strategy that can be applied across the spectrum of available applications.
Most recent Debt/Equity Ratio greater than the median industry average: High debt/equity ratio implies high leverage. High leverage indicates a huge level of repayment that the company has to make in connection with the debt amount.
Through a wide variety of mobile applications, we’ve developed a unique visual system and strategy that can be applied across the spectrum of available applications.
A strategy is a general plan to achieve one or more long-term.
UI/UX Design, Art Direction, A design is a plan or specification for art.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Quis ipsum suspendisse ultrices gravida. Risus commod viverra maecenas accumsan lacus vel facilisis. ut labore et dolore magna aliqua.

There are always some stocks, which illusively scale lofty heights in a given time period. However, the good show doesn’t last for these overblown toxic stocks as their current price is not justified by their fundamental strength.
Toxic companies are usually characterized by huge debt loads and are vulnerable to external shocks. Accurately identifying such bloated stocks and getting rid of them at the right time can protect your portfolio.
Overpricing of these toxic stocks can be attributed to either an irrational enthusiasm surrounding them or some serious fundamental drawbacks. If you own such bubble stocks for an inordinate period of time, you are bound to see a massive erosion of wealth.
However, if you can precisely spot such toxic stocks, you may gain by resorting to an investing strategy called short selling. This strategy allows one to sell a stock first and then buy it when the price falls.
While short selling excels in bear markets, it typically loses money in bull markets.
So, just like identifying stocks with growth potential, pinpointing toxic stocks and offloading them at the right time is crucial to guard one’s portfolio from big losses or make profits by short selling them. Heska Corporation HSKA, Tandem Diabetes Care, Inc. TNDM, Credit Suisse Group CS,Zalando SE ZLNDY and Las Vegas Sands LVS are a few such toxic stocks.Screening Criteria
Here is a winning strategy that will help you to identify overhyped toxic stocks:
Most recent Debt/Equity Ratio greater than the median industry average: High debt/equity ratio implies high leverage. High leverage indicates a huge level of repayment that the company has to make in connection with the debt amount.
Through a wide variety of mobile applications, we’ve developed a unique visual system and strategy that can be applied across the spectrum of available applications.
A strategy is a general plan to achieve one or more long-term.
UI/UX Design, Art Direction, A design is a plan or specification for art.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Quis ipsum suspendisse ultrices gravida. Risus commod viverra maecenas accumsan lacus vel facilisis. ut labore et dolore magna aliqua.
There are always some stocks, which illusively scale lofty heights in a given time period. However, the good show doesn’t last for these overblown toxic stocks as their current price is not justified by their fundamental strength.
Toxic companies are usually characterized by huge debt loads and are vulnerable to external shocks. Accurately identifying such bloated stocks and getting rid of them at the right time can protect your portfolio.

Overpricing of these toxic stocks can be attributed to either an irrational enthusiasm surrounding them or some serious fundamental drawbacks. If you own such bubble stocks for an inordinate period of time, you are bound to see a massive erosion of wealth.
However, if you can precisely spot such toxic stocks, you may gain by resorting to an investing strategy called short selling. This strategy allows one to sell a stock first and then buy it when the price falls.
While short selling excels in bear markets, it typically loses money in bull markets.
So, just like identifying stocks with growth potential, pinpointing toxic stocks and offloading them at the right time is crucial to guard one’s portfolio from big losses or make profits by short selling them. Heska Corporation HSKA, Tandem Diabetes Care, Inc. TNDM, Credit Suisse Group CS,Zalando SE ZLNDY and Las Vegas Sands LVS are a few such toxic stocks.Screening Criteria
Here is a winning strategy that will help you to identify overhyped toxic stocks:
Most recent Debt/Equity Ratio greater than the median industry average: High debt/equity ratio implies high leverage. High leverage indicates a huge level of repayment that the company has to make in connection with the debt amount.
The training provided by universities in order to prepare people to work in various sectors of the economy or areas of culture.
Higher education is tertiary education leading to award of an academic degree. Higher education, also called post-secondary education.
Secondary education or post-primary education covers two phases on the International Standard Classification of Education scale.
Google’s hiring process is an important part of our culture. Googlers care deeply about their teams and the people who make them up.
A popular destination with a growing number of highly qualified homegrown graduates, it's true that securing a role in Malaysia isn't easy.
The India economy has grown strongly over recent years, having transformed itself from a producer and innovation-based economy.
Google’s hiring process is an important part of our culture. Googlers care deeply about their teams and the people who make them up.
A popular destination with a growing number of highly qualified homegrown graduates, it's true that securing a role in Malaysia isn't easy.
The India economy has grown strongly over recent years, having transformed itself from a producer and innovation-based economy.
The training provided by universities in order to prepare people to work in various sectors of the economy or areas of culture.
Higher education is tertiary education leading to award of an academic degree. Higher education, also called post-secondary education.
Secondary education or post-primary education covers two phases on the International Standard Classification of Education scale.
The education should be very interactual. Ut tincidunt est ac dolor aliquam sodales. Phasellus sed mauris hendrerit, laoreet sem in, lobortis mauris hendrerit ante.
The education should be very interactual. Ut tincidunt est ac dolor aliquam sodales. Phasellus sed mauris hendrerit, laoreet sem in, lobortis mauris hendrerit ante.
The education should be very interactual. Ut tincidunt est ac dolor aliquam sodales. Phasellus sed mauris hendrerit, laoreet sem in, lobortis mauris hendrerit ante.
The education should be very interactual. Ut tincidunt est ac dolor aliquam sodales. Phasellus sed mauris hendrerit, laoreet sem in, lobortis mauris hendrerit ante.
The education should be very interactual. Ut tincidunt est ac dolor aliquam sodales. Phasellus sed mauris hendrerit, laoreet sem in, lobortis mauris hendrerit ante.
The education should be very interactual. Ut tincidunt est ac dolor aliquam sodales. Phasellus sed mauris hendrerit, laoreet sem in, lobortis mauris hendrerit ante.
All the Lorem Ipsum generators on the Internet tend to repeat predefined chunks as necessary
1 Page with Elementor
Design Customization
Responsive Design
Content Upload
Design Customization
2 Plugins/Extensions
Multipage Elementor
Design Figma
MAintaine Design
Content Upload
Design With XD
8 Plugins/Extensions
All the Lorem Ipsum generators on the Internet tend to repeat predefined chunks as necessary
5 Page with Elementor
Design Customization
Responsive Design
Content Upload
Design Customization
5 Plugins/Extensions
Multipage Elementor
Design Figma
MAintaine Design
Content Upload
Design With XD
50 Plugins/Extensions
All the Lorem Ipsum generators on the Internet tend to repeat predefined chunks as necessary
10 Page with Elementor
Design Customization
Responsive Design
Content Upload
Design Customization
20 Plugins/Extensions
Multipage Elementor
Design Figma
MAintaine Design
Content Upload
Design With XD
100 Plugins/Extensions

SEO services are the backbone of any performance-driven digital marketing strategy. For agencies and professionals in the SEO space, offering well-defined SEO services is essential to help clients improve visibility, attract organic traffic, and increase conversions. From on-page optimization to technical audits and white-label SEO software, the landscape of SEO services covers a wide range of techniques that help businesses adapt to search algorithms and user intent.
In this guide, you will learn what SEO services include, why they matter for agencies, the leading types of services clients look for, specialized offerings like on-page SEO services and ecommerce SEO services, and how to use tools like SEO reporting software to deliver transparent client results. We’ll also explore services tailored for niche industries such as dental practices, examine pricing structures for agencies, and highlight key trends shaping how SEO is delivered in 2026 and beyond. This article is crafted for SEO professionals, digital marketers, and agency owners aiming to expand their portfolios, streamline delivery, and retain long-term clients through high-value SEO offerings.
SEO services refer to a suite of strategies designed to improve a website’s visibility in search engines like Google, Bing, and Yahoo. These services can be offered individually or as part of a comprehensive SEO strategy. Some key services include keyword research, on-page optimization, technical audits, content strategy, link building, and ongoing performance monitoring. Effective SEO services help businesses improve their ranking in search results, driving organic traffic and boosting conversions.
SEO services are essential for agencies as they provide measurable value to clients by increasing website visibility, enhancing user experience, and improving brand credibility. For agencies, understanding the full scope of SEO services is key to offering comprehensive solutions that drive long-term growth and measurable results.
SEO services matter for agencies because they provide a roadmap for client success in an ever-evolving digital landscape. Agencies that offer SEO services can:
Offering SEO services is an effective way to build lasting relationships with clients and deliver tangible results. Through ongoing optimization, SEO agencies can ensure that clients stay ahead of their competitors and maintain strong visibility across search engines.

Organic SEO refers to the process of optimizing a website without paid advertisements to improve rankings in search results. It focuses on keyword research, quality content, and authoritative link building. Organic SEO requires a long-term approach, but it ultimately provides the most sustainable traffic. Agencies can offer organic SEO by crafting content that answers user queries, optimizing on-page elements like headings and meta descriptions, and building quality backlinks.
On-page SEO involves optimizing individual web pages to rank higher in search engines. This includes content optimization, keyword targeting, internal linking, and the use of header tags. The goal of on-page SEO is to ensure that each page provides valuable, relevant content that aligns with user intent. By optimizing elements like title tags, images, and metadata, agencies can improve both search engine rankings and user experience.
Technical SEO focuses on the infrastructure of a website, ensuring that it is technically sound for search engines to crawl and index. This includes optimizing site speed, ensuring mobile responsiveness, implementing schema markup, and improving site architecture. Technical SEO is crucial for a website’s performance and plays a large role in enhancing user experience.
Local SEO is aimed at helping businesses appear in local search results, especially for services and businesses with physical locations. This service includes optimizing Google My Business profiles, managing local citations, and targeting location-specific keywords. Local SEO is essential for small businesses such as restaurants, law firms, and healthcare providers who rely on foot traffic or local clientele.
International SEO helps businesses expand their reach globally by optimizing websites for international search engines. Agencies offering international SEO services optimize content for multiple languages, regions, and cultures. This can involve setting up hreflang tags, using country-specific domains, and conducting market-specific keyword research.
White-label SEO software and services are essential tools for agencies looking to scale their offerings. These tools allow agencies to brand and resell SEO services under their own name without the need to develop in-house software or services. White-label SEO software typically includes features like ranking tracking, backlink analysis, and performance reports that can be branded and sent directly to clients.
By using white-label SEO solutions, agencies can focus on their core business activities while providing high-quality, professional SEO reports and services to their clients. This enables agencies to offer more services without increasing overhead.
An SEO audit is a comprehensive evaluation of a website’s performance, identifying issues that could affect its rankings and visibility. SEO audit services often cover:
SEO audits are a great way for agencies to pinpoint areas for improvement and offer actionable recommendations that can immediately impact client performance.
SEO reporting software is crucial for tracking performance and providing clients with transparency. Effective SEO reporting tools allow agencies to track rankings, analyze traffic sources, monitor backlink growth, and measure the ROI of SEO efforts. Some popular SEO reporting tools include Google Analytics, SEMrush, Ahrefs, and Moz.
Best practices for SEO reporting include:
Using the right SEO reporting software ensures that agencies can provide valuable insights into client campaigns and adjust strategies accordingly.
Having a standard SEO report template helps agencies save time while delivering consistent, professional reports. A well-crafted SEO report template should include:
A good SEO report template helps agencies maintain transparency and provide clients with the insights they need to make informed decisions about their digital strategy.
eCommerce websites face unique challenges in SEO due to the volume of products and pages they must optimize. eCommerce SEO services include optimizing product pages, improving site navigation, and using schema markup to enhance product visibility in search results. Agencies offering eCommerce SEO services help clients attract targeted traffic, improve sales, and enhance product discoverability.
Some strategies include:
Effective eCommerce SEO results in higher visibility, increased traffic, and ultimately more sales for online retailers.
Dentists and other local services rely heavily on local SEO services to drive traffic from local searches. Optimizing for local search involves:
Local SEO is essential for dental practices that want to appear in local search results and attract patients from their immediate geographic area.
When selecting an SEO agency, businesses should consider several factors:
An affordable SEO agency should provide high-quality services without breaking the bank.
SEO companies typically structure their pricing based on the scope of work and client needs. Common pricing models include:
Pricing varies depending on the complexity and scale of the SEO strategy, but transparent pricing ensures clients understand what they are paying for and the expected results.
SEO case studies provide evidence of an agency’s success in improving search rankings, traffic, and conversions. Agencies can use case studies to showcase their expertise, build credibility, and attract new clients. Case studies should detail the challenges, strategies implemented, and results achieved. Successful case studies help establish trust and prove that the agency can deliver results.

Some common SEO mistakes agencies should avoid include:
Avoiding these mistakes ensures a more effective and sustainable SEO strategy.
As technology continues to advance, AI-driven search, voice search optimization, and answer engine optimization are transforming SEO practices. Agencies that adapt to these changes will stay ahead of the competition and continue to deliver valuable SEO services to clients. Monitoring trends and adjusting strategies accordingly is key to maintaining SEO success in the future.
SEO services are an essential part of any digital marketing strategy. For agencies, offering structured, measurable, and strategic SEO services builds trust with clients and drives long-term growth. Whether you’re specializing in white-label solutions, local niches like dental SEO, or global campaigns, the principles of quality SEO remain consistent: focus on relevance, performance, and transparent results. By embracing these practices, SEO agencies can expand their service offerings, retain clients, and stay competitive in a rapidly changing digital world.
1. What exactly do SEO services include?
SEO services include keyword research, on-page optimization, technical audits, content strategy, link building, and reporting.
2. How does white-label SEO benefit agencies?
White-label SEO allows agencies to resell and brand SEO work done by third parties, saving time and investment.
3. Why is local SEO important for dentists?
Local SEO helps dentists show up in local search results and Google Map Pack searches for terms like “dentist near me.”
4. What does an SEO audit report show?
An SEO audit highlights site issues, technical flaws, content gaps, and opportunities that impact search rankings.
5. How long does SEO take to show results?
SEO gains typically appear in 3–6 months but depend on competition and strategy execution.

Powerful Turnkey Backlink Solutions to Boost Client Rankings & Retention
In today’s competitive SEO landscape, high-quality backlinks remain one of the biggest drivers of organic rankings. But for many digital agencies and SEO specialists, building those links in-house is a major time and resource sink. That’s where white label link building services come into play — a scalable, SEO-centric way to deliver authoritative backlinks for your clients without hiring, training, or managing your own outreach team.
In this guide, we’ll unpack everything Aussie agencies and SEO pros need to know about white label link building: what it is, how it works, the types of link placements you can resell, the benefits and risks involved, and practical tips to get the best ROI. Whether you’re running an off-page SEO service, looking to retain more clients, or aiming to scale your agency offerings, this article gives you a strategic edge with examples, insights and actionable strategies. Natural, ethical link acquisition remains the gold standard for long-term SEO success — and white label solutions can help you deliver this under your own brand.
Definition & how it works:
White label link building services are outsourced backlink acquisition solutions that SEO agencies, consultants or digital marketers resell under their own brand banner. Instead of building links yourself — i.e., prospecting sites, managing outreach, negotiating guest posts, and reporting results — a white label partner handles the heavy lifting and delivers the outcomes to you unbranded.
In practice, a third-party link building provider generates contextual backlinks (like guest articles and niche placements) on real, high-authority sites. They then hand over reports, tracking data and live links that you can present directly to your clients as if they came from your agency.
Key stages of the process:
This full-service model lets agencies scale without increasing internal SEO labour.
Trying to manage link outreach yourself is time-intensive. Agencies often juggle client SEO campaigns, content creation, analytics, and strategy — so outsourcing the link building frees up valuable hours that can be used on growth, strategy meetings or upselling.
Unlike hiring and training junior SEO staff, a white label partner comes with expertise, tools and publisher connections. This lets you take on more clients without ballooning employment costs.
Good white label services prioritise relevant, high-authority backlinks — from niche sites that can help clients rank for their key terms. It’s cheaper and faster than building relationships from scratch.
When a white label vendor provides custom reports under your logo and delivers outcomes, clients see consistency. They don’t know the work was outsourced — boosting your agency’s credibility.
Guest post backlinks remain highly effective. These are editorial links placed within articles published on external, niche-relevant websites. High DA/DR guest posts send strong ranking signals to Google.
This is where links are inserted into existing, indexed content that’s already ranking. Because the content already exists and drives traffic, these can boost SEO impact quicker than brand new posts.
Lists or curated resources that include your client’s link are low-effort but can be powerful contextual signals when relevant.
Earned links from news sites and high-authority blogs via PR campaigns can improve trust and brand visibility — and they fit well into long-term SEO plans.
Always ask for sites with strong Domain Authority (DA), Domain Rating (DR) and real traffic — not link farms or auto-generated networks.
Manual outreach delivers higher acceptance rates and genuine placements. Automation might look cheap but often harms quality.
You want clear reports that include live URLs, anchor text details, and metrics you can present to clients without awkward explanations.
A handful of contextual links in your client’s niche often beats dozens of irrelevant links that don’t impact rankings.

Avoid providers that deliver links from low-trust networks, PBNs, or spammy sites — these can trigger Google penalties.
Always verify that link building methods are white-hat — manual outreach, editorial placements, and genuine opportunities rather than automated schemes.
Make sure the strategy matches your client’s goals — keyword focus, target market, and industry niche — otherwise the efforts may not deliver results.
White label link building pricing can be structured as:
Each model has pros and cons depending on your agency size and client load.
To add value and maximise profitability:
White label link building services have become indispensable for Australian SEO agencies, off-page specialists, and digital marketers who want to scale without ballooning costs or internal teams. By partnering with skilled backlink providers, you get access to manual outreach expertise, high-authority placements and branded reporting that strengthens your offerings and drives real results for your clients.
The key to success lies in choosing partners that prioritise relevance, transparency, and ethical link acquisition. Whether you’re adding link building to your SEO packages for the first time, or you’re scaling multiple campaigns, white label solutions offer flexibility and capacity without the overhead of in-house operations.
Remember: link building isn’t just about counting backlinks — it’s about genuine endorsements from relevant, authoritative sites that align with your client’s niche and target keywords. With the right strategy and provider, your agency can boost rankings, increase traffic, and keep clients engaged long-term. Ready to grow your SEO services with high-impact link building? Let’s get started!
Q1. What makes white label link building different from regular SEO link building?
White label services are outsourced and rebranded — you sell them as your own, whereas regular link building might be in-house or client-facing directly.
Q2. How long until clients see results from backlinks?
SEO benefits often appear within 2–6 months, depending on niche competition and authority of the backlinks.
Q3. Are white label links safe for Google rankings?
Yes, if they are acquired via white-hat, manual outreach and placed on relevant, high-authority domains. Avoid automation/PBNs.
Q4. Can I customise link strategies for different clients?
Good providers allow tailored approaches based on industry, keyword targets, and budget.
Q5. What metrics should agencies track for link campaigns?
Track DA/DR of placements, organic traffic growth, keyword rankings, and referral traffic.

The world of crypto investing is evolving fast — and 2025 may be the year defining how mainstream money views Ethereum. With the approval and launch of several spot and futures‑based exchange‑traded funds tied to Ethereum (ETH), more investors now have a simple, regulated route to gain ETH exposure — without wrestling with wallets, private keys, or manual crypto trades.Read another guide on meta mask wallet.
In this guide, we dive deep into ethereum etf eth: what these funds are, how they work, why they matter, and how they influence both the price of ETH and the broader crypto market. Whether you’re an altcoin trader, long‑term HODLer, or just crypto‑curious, by the end you’ll understand the leading ETH ETFs, their pros and cons, and how to decide what fits your strategy. Let’s build a roadmap for trading, investing, and thinking about ETH through the lens of ETFs.
An Ethereum ETF (or “Ethereum ETF ETH”) is a financial instrument — a fund — that gives you exposure to Ethereum’s native token (ETH) without you owning the token directly. Instead, a fund manager buys and holds ETH (or derivatives tied to ETH), then issues ETF shares that trade on traditional stock exchanges. As the price of ETH fluctuates, the value of the ETF shares typically moves in tandem, offering a familiar “stock-like” way to gain from crypto price action. CoinDesk+1
Many early ETH ETFs were futures-based, but with regulatory shifts and growing demand, spot ETH ETFs have gained prominence — offering “true” ETH exposure without needing to manage wallets or private keys. Ledger+1
For many retail investors, trading on a crypto exchange and dealing with crypto wallets, security, private keys, and gas fees can be intimidating. An ETH ETF simplifies this: you just need a brokerage account — the same you use for stocks. That lowers the technical barrier and reduces the friction between traditional finance and crypto. CoinDesk+1
Moreover, ETFs bring regulatory clarity, easier liquidity, and the ability to hold ETH exposure inside traditional tax‑sheltered or retirement accounts (in jurisdictions that allow it). For institutions — hedge funds, pension funds, family offices — ETFs offer a regulated, auditable, and compliant vehicle to add ETH to their portfolios. Cointelegraph+1
In short: Ethereum ETFs serve as a bridge between the traditional financial world and the crypto world — making ETH accessible to a far broader audience while preserving regulatory compliance, liquidity, and ease of access.
Unique Insight: For many in emerging markets (including Asia), ETFs may eventually become the primary gateway to crypto exposure — because they bypass regulatory uncertainties around crypto exchanges and make crypto investable through legacy financial infrastructure.
To appreciate why ETH ETFs are suddenly a big deal, we need to look at key milestones — especially in 2023–2025.
While some funds tied to Ethereum already existed in ETF‑like wrappers, many were based on futures contracts rather than actual ETH. For example, certain ETFs launched in late 2023 invested in ETH futures instead of spot crypto. SEC+1
In parallel, major financial institutions — including large asset managers — began filing formal applications for spot ETH ETFs, signaling growing confidence in regulatory approval and institutional demand for direct ETH exposure. CoinDesk+1
The real turning point came in 2024, when the regulator greenlit spot-based ETH ETFs. According to major coverage, spot Ethereum ETFs were approved for listing, allowing funds to hold actual ETH rather than derivatives. CoinDesk+1
With this approval, the path was cleared for mainstream ETH investment via traditional capital markets. Investors no longer needed to rely on crypto exchanges — they could buy ETH exposure as easily as buying a stock or conventional ETF share.
The regulatory approval and ETF launch didn’t just democratize access — they triggered a wave of institutional capital. According to recent data, inflows into spot ETH ETFs have surged, fueling renewed interest in ETH across traditional investment circles. NFT Evening+2ChainAffairs+2
Analysts argue that this increased institutional adoption could reshape ETH’s supply-demand dynamics, reduce reliance on volatile crypto exchanges, and further integrate Ethereum into mainstream finance. Cointelegraph+1
Not all ETH ETFs are created equal. Some stand out because of fees, liquidity, issuer reputation, or investor trust. As of 2025, here are some of the major spot ETH ETFs gaining traction. Ledger+1
| ETF Name (Symbol) | Issuer / Sponsor | Fee / Expense Ratio* |
|---|---|---|
| iShares Ethereum Trust (ETHA) | BlackRock | 0.12% (waived for first 12 months), then ~0.25% Ledger |
| VanEck Ethereum Trust (ETHV) | VanEck | 0% initial free‑period, then ~0.20% Ledger |
| Fidelity Ethereum Fund (FETH) | Fidelity | 0% until 2025, then ~0.25% Ledger |
| Bitwise Ethereum ETF (ETHW) | Bitwise | 0% for first 6 months, then ~0.20% Ledger |
| Other funds: 21Shares Core ETH (CETH), Invesco Galaxy ETH (QETH), Franklin Ethereum Trust (EZET), Grayscale Ethereum Mini Trust (ETH), Grayscale Ethereum Trust (ETHE) | Various issuers | Fees vary; generally between 0.15%–0.25% after initial waiver periods. Ledger |
*Fees and waivers can vary over time; always check the latest fund filings for up-to-date expense ratio details.
Strategic Insight: If you’re entering ETH exposure via ETF, choosing a high‑liquidity, low‑fee, and well‑known issuer reduces slippage risk, makes redemptions easier, and ensures better tracking of ETH price.
Many crypto newcomers — and even seasoned investors — find self-custody of ETH complex and risky. Wallet security, private keys, gas fees, network congestion, and the general hassle can deter participation. An ETH ETF wraps all that complexity into a familiar instrument: buy/sell shares via a brokerage account. No keys, no wallet, no transfers. It’s a simple, regulated, and accessible entry point. CoinDesk+1
ETFs operate under established financial regulations, offering oversight, transparency, and investor protection. For institutions — hedge funds, pension funds, family offices — compliance matters. With ETH ETFs now approved and trading, ETFs provide a regulated route to add ETH exposure to traditional portfolios. This helps bridge the gap between traditional finance and the crypto world. CoinDesk+1
ETFs offer high liquidity: you can buy or sell shares during market hours, potentially with tighter spreads compared to some crypto exchanges. This makes ETH ETFs useful for both long‑term holders and short-term traders or speculators.
Moreover, institutional players often prefer ETFs because they align with familiar investment systems and compliance regimes. The inflows in 2025 — often in hundreds of millions per day — show that large capital is rotating into ETH through ETFs. NFT Evening+2FinOracle+2
With an ETF, you don’t need to understand the intricacies of staking, liquidity pools, wallet security, or DeFi protocols. You get price exposure to ETH. For investors wanting simplicity and avoiding technical complexity — especially in volatile markets — that’s attractive. For many retail and institutional investors, ETFs represent the “low friction” path to crypto exposure.
As ETFs accumulate ETH, demand rises while available supply on exchanges shrinks. That creates supply pressure — especially if inflows are large and sustained. This dynamic has played out in 2025: major net inflows into ETH ETFs have coincided with ETH price rallies. NFT Evening+2FinOracle+2
For instance, one report showed that entire spot ETH ETFs had amassed over $12.1 billion in AUM by mid-2025. NFT Evening As ETF demand grows, circulating supply available for trading becomes scarcer, which can, in theory, put upward pressure on price — especially in bullish markets.
In early June 2025, ETH recovered strongly — bouncing from ~$2,460 to above $2,500 — amid notable inflows to ETFs. Specifically, one fund saw nearly $492 million in net inflows that week, signaling growing institutional demand and renewed confidence. CoinDesk
This suggests that, for traders and investors, monitoring ETF flow data can offer a predictive edge: major inflows may precede price spikes, while large outflows or fund redemptions might indicate potential pullbacks.
As more ETH moves into ETFs — held in long-term custody by institutions — less ETH remains on exchanges or in retail hands. That could lead to reduced on-chain liquidity, fewer tokens available for staking or DeFi, and a generally tighter supply environment. Combined with growing demand from institutions, this dynamic could favor medium- to long‑term bullishness for ETH’s price.
Unique Perspective: ETFs might contribute to a structural shift in how Ethereum is held — fewer retail traders, more institutional “vaults.” Over time, this could influence not just price, but Ethereum’s macro supply‑demand dynamics, network utility (staking and DeFi participation), and even its role as a global digital asset.
ETF exposure brings benefits — but also trade‑offs and risks. It’s critical to understand them before investing heavily.
ETH remains a volatile asset. Even with ETF backing, share prices will reflect ETH’s market swings. Large inflows can drive surges — but sentiment turn, macroeconomic shocks, or regulatory news can trigger abrupt drawdowns. As with any crypto investment: gains may be big, but so can losses.
While ETFs offer regulatory clarity compared to many crypto exchanges, they still rely on custodians to hold ETH securely. Custody risk — though mitigated — remains. Moreover, changes in regulation, compliance requirements, or legal treatment of crypto could impact ETF operations or eligibility. cyberstone.com.tr+1
One major trade‑off: ETFs typically do not stake their holdings (at least as of now), meaning ETF investors miss out on staking yields (which for ETH might be 3–6% annually or more). Also, ETF investors cannot participate directly in decentralized applications (DeFi), smart‑contract protocols, or governance. In other words: you get price exposure, not utility exposure.
For long-term believers in Ethereum’s utility and ecosystem growth — not just price — this could be a significant drawback compared with holding ETH directly.
As ETH becomes widely held via ETFs, it gains institutional legitimacy — which can help bring more capital into the broader crypto ecosystem. Pension funds, family offices, and corporate treasuries may begin viewing ETH as a legitimate asset class. That could lead to increased interest not only in ETH, but in altcoins, DeFi projects, and Layer‑2 ecosystems.
This may also improve liquidity and reduce volatility over time as institutional players allocate significant capital and hold ETH long term, rather than trading frequently.
On the flip side, if large amounts of ETH are locked inside ETFs and not staked, this could reduce the overall staking supply and shift the balance between liquid supply and staked ETH. That might affect staking yields, validator economics, and the broader DeFi ecosystem.
This dynamic raises a key question: will future ETH ETFs seek to incorporate staking (or stake-enabled ETPs)? If so, that could reshape the entire landscape — merging price exposure with utility yield.
Heavy institutional accumulation via ETFs often removes ETH from exchange inventories. Reduced exchange supply can tighten liquidity, potentially making ETH more prone to sharp price swings — both up and down — based on demand, news, or macro events.
Unique Insight: Over time, ETFs could contribute to a structural re‑distribution of ETH — from retail exchanges and wallets to institutional vaults. This might erase some of the “traditional retail volatility,” but could also create a fragile market: if many ETF holders decide to redeem simultaneously, or if sentiment shifts, liquidity could dry up quickly.
If your aim is to accumulate ETH exposure over months or years, look for ETFs with low long‑term fees, strong issuer reputation, high liquidity, and minimal tracking error. In that sense, funds like ETHA (BlackRock) or ETHV (VanEck) make sense.
Also consider: do you prefer maximum ETH exposure (even if no staking yield), or are you willing to accept some trade‑offs for convenience and regulatory clarity? ETFs are ideal for simple exposure without worrying about keys or wallets.
If you trade ETH based on market cycles, ETF inflows, or macro events — ETFs can offer liquidity and easy entry/exit. Keep an eye on flow data, exchange reserves, and technical levels. ETF flows can act as a leading indicator for price momentum.
However, manage risk carefully: tracking error, premium/discount effects, and fund redemptions can work against traders. Use stop‑losses or hedging if possible.
If you’re building a diversified portfolio with both traditional assets and crypto — ETFs provide a clean, compliant way to add ETH exposure. For institutions, compliance, auditability, and regulatory clarity often matter more than maximizing staking yield or DeFi participation.
In that case, choose a reputable ETF with large AUM, transparent auditing, and tight spreads — and consider how ETH exposure fits into your overall risk-return profile.
One of the biggest hopes in the cryptocurrency world is the arrival of ETFs that not only hold ETH but also stake it, passing staking yields to investors. As regulators and exchanges adapt, it’s plausible that by late 2025 or 2026, some funds might propose staking-enabled ETPs. This could fundamentally change the value proposition — combining price exposure and yield generation. cyberstone.com.tr+1
While much of the early adoption has happened on U.S. exchanges, international institutions and investors — especially in Asia, Middle‑East, and emerging markets — may increasingly view ETH ETFs as a way to get exposure without dealing with local exchange regulatory hurdles. The ripple effect could expand demand globally, adding pressure on global ETH supply.
Regulation remains a variable. While current laws and approvals have enabled spot ETH ETFs, future changes — new laws, taxes, compliance burdens, or macroeconomic shocks — could impact ETF demand. Investors must remain alert.
Also, as ETFs grow, regulators worldwide may impose new rules—e.g., restrictions on staking, redemption limits, or reporting requirements. The next 2–3 years may see intense scrutiny as institutions accumulate crypto en masse.
If institutional capital continues to flow, and ETF adoption broadens globally, ETH could undergo a structural transformation: from a largely retail-held token to a mainstream institutional asset — a kind of “digital commodity.” That could tighten supply, reduce velocity, and potentially support new price floors, especially during broader crypto cycles.
To help readers digest complex ideas and data, here are three custom‑image / infographic concepts you could embed in the final article:
These visuals help readers — especially those coming from trading / technical / institutional backgrounds — grasp how ETH ETFs differ and why they matter.
The arrival of ethereum etf eth as a mainstream, regulated investment vehicle marks one of the biggest inflection points in crypto’s history. What was once limited to wallet‑holders and exchange users is now accessible to anyone with a brokerage account. For traders and altcoin enthusiasts, this could mean easier ETH exposure, better liquidity, and the ability to diversify within a broader portfolio — all without wrestling with private keys or gas fees.
At the same time, the inflows from institutions could reshape supply‑demand dynamics for ETH: less supply on exchanges, more ETH locked in funds, and potentially tighter price floors. However, the trade‑off is clear: ETFs strip away the key utility of ETH — staking and DeFi participation. Plus, regulatory and custody risks remain, and investors must accept that returns may lag a “naked” ETH holding.

I am available for freelance work. Connect with me via and call in to my account.
Phone: +923036256933 Email: admin@sahasibloggers.comHello
No WhatsApp Number Found!
WhatsApp us